Collaborative Lifecycle Management (CLM) has directly supported two types of single sign-on (SSO) authentication for some time. First, all applications installed in the same application server (whether IBM WebSphere Application Server or Tomcat) automatically share login sessions, such that if you log in to one application, you are also logged into all the other applications deployed in the same server. Second, when all applications are deployed in one or more WebSphere Application Servers, you can configure Lightweight Third Party Authentication (LTPA) SSO so that login sessions are shared across all the WebSphere servers.
We are excited to announce that we have added two new SSO options in the CLM 6.0 release. You’ll now have the option to use either Kerberos authentication, or what we call “Jazz Security Architecture Single Sign-On”, which is based on the OpenID Connect standards.
Kerberos is a well-established SSO protocol that is also the default authentication protocol used by Microsoft Windows, so if your organization uses Windows workstations, Microsoft Active Directory for user management, and deploy Jazz applications in WebSphere 8 or later, it will be possible to configure CLM so that your Windows login session is automatically used to log in to CLM. Kerberos can also be used with non-Windows workstations, as long as you use a Microsoft Active Directory server to manage your user accounts. While it has been possible to configure CLM servers to use Kerberos for some time, only web browser clients could take advantage of Kerberos login sessions – the RTC Eclipse client, the Microsoft Visual Studio RTC client, the other Windows .NET clients, the RTC build engine and clients, and the various command-line clients could not use Kerberos. Now, all those RTC clients will work with Kerberos. See Single sign-on authentication in CLM for the complete list of RTC clients that support Kerberos, and Configuring Kerberos for details on setting up Kerberos for CLM.
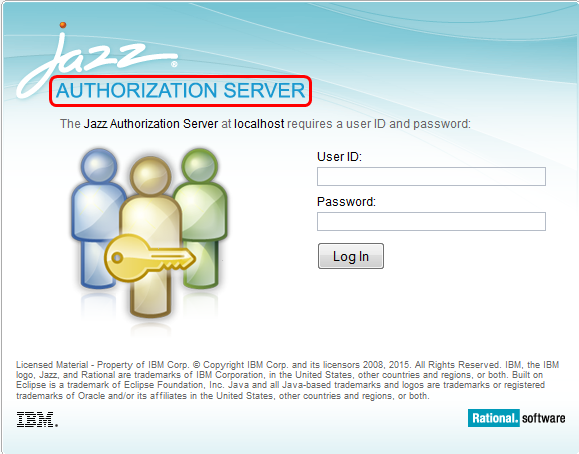
The OpenID Connect (OIDC) authentication protocol was established in early 2014 as an extension of the OAuth 2.0 protocol, designed to be easier to adopt across a wide range of clients (native applications, browsers, browser-based applications, and mobile devices). It is extensible and configurable (with optional features). Jazz Security Architecture (JSA) is a particular profile of OIDC, specifying which optional features are included, and a few extensions. Authentication is handled by the Jazz Authorization Server (JAS); Jazz applications delegate to that server instead of relying on the application server to handle authentication. Single sign-on is supported across all applications that are configured to use the same JAS, independent of what sort of application servers they are deployed in, and what platform they are running on. To use Jazz Security Architecture SSO, you must install the Jazz Authorization Server, configure it and start it up, and either enable JSA SSO in CLM applications when installing (for a new installation), or enable JSA SSO after upgrading to the 6.0 release (for existing installations).
The login form for the JAS looks very similar to the Jazz application login form, but you’ll know that you’re using the JAS for authentication if the login form says “AUTHORIZATION SERVER” instead of “TEAM SERVER”:
You can find more information on how authentication works in general, and the various options available, in the Jazz Server Authentication Explained article. We’re hoping these new SSO options provide increased flexibility and ease-of-use for our users.
Be sure visit us [at booth #203] at Agile 2015 to experience IBM’s DevOps solutions for collaborative development, continuous testing and continuous release & deployment. For more details see: http://agile2015.agilealliance.org/
John Vasta
Senior Software Engineer