Updating Client Registration Data In Jazz Authorization Server
Authors: ShubjitNaikBuild basis: IBM Engineering Lifecycle Management and Jazz Authorization Server 7.x
When IBM Engineering Lifecycle Management Solution (ELM) is deployed with Jazz Authorization Server (JAS), for each ELM application there is a client registration in JAS. The registration contains details such as ClientId, ClientSecret, Redirect URIs etc and the URL to retrieve the data from JAS is
Following are the instructions to update ClientSecret for JTS application.
https://JazzAuthServerURI/oidc/endpoint/jazzop/registration.
There are instances where the ClientSecret or RedirectURI for a registered application needs to be changed. Example , when you migrate an application from one JAS server to another or when you see the following error accessing an ELM application: error_code: _invalid_client_credentials error_message: CRJSA0009E The single sign-on authentication did not succeed because of an application error. error_message_explanation: The authentication process could not be completed because of a problem with the application. The application might be violating a protocol or using an underlying single sign-on library incorrectly. error_message_useraction: For details about the cause of the error, check the log files for the application and the authorization server.The focus of this article is to share methods on updating Client registration data like ClientSecret in JAS and ELM applications
Note: These instructions do not apply for LQE and LDX as the properties file does not include the ClientId and Secret value
Update the Client Secret for application in JAS
Update Client Secret Using JAS CLI
Jazz Authorization Server has bundled CLI tools which helps in management of Client registrations. Following are the steps to update ClientSecret for Jazz Team Server (JTS) application. First find the ClientId for the JTS application- You can either load the URL
https://JazzAuthServerURI/oidc/endpoint/jazzop/registrationand search for the value of the parameterclient_idunder client nameJazz Team Server - OR on the JTS server view the file
[JTS_HOME]\server\conf\jts\teamserver.propertiesand search forcom.ibm.team.repository.servlet.sso_clientId - Lets assume the ClientId for JTS application is
bd23ca7b376b4bb7a17680a496048473
- On the JAS server
- Change directory to
[JAS_HOME]\cliand run the following command./lsclient -a https://JazzAuthServerURI/oidc/endpoint/jazzop -u [AdminUser]:[AdminPassword] bd23ca7b376b4bb7a17680a496048473 >& jts.json
- Here is a sample exported file, we would see one such entry per application.
[ { "functional_user_groupIds" : [ "JazzAdmins" ], "trusted_uri_prefixes" : [ "https://localhost:9443/jts/", "https://elm.example.org/jts/", "https://127.0.0.1:9443/jts/" ], "post_logout_redirect_uris" : [ "https://127.0.0.1:9443/jts/service/com.ibm.team.repository.service.internal.ILogoutRestService", "https://elm.example.org/jts/service/com.ibm.team.repository.service.internal.ILogoutRestService", "https://localhost:9443/jts/service/com.ibm.team.repository.service.internal.ILogoutRestService" ], "grant_types" : [ "authorization_code", "client_credentials", "implicit", "refresh_token", "urn:ietf:params:oauth:grant-type:jwt-bearer" ], "subject_type" : "public", "application_type" : "web", "allow_regexp_redirects" : false, "registration_client_uri" : "https://JazzAuthServerURI/oidc/endpoint/jazzop/registration/bd23ca7b376b4bb7a17680a496048473", "redirect_uris" : [ "https://localhost:9443/jts/jsa", "https://localhost:9443/jts/jsa?confirm=true", "https://prod02.example.com:9443/jts/jsa", "https://elm.example.org/jts/jsa?confirm=true", "https://127.0.0.1:9443/jts/jsa", "https://127.0.0.1:9443/jts/jsa?confirm=true" ], "token_endpoint_auth_method" : "client_secret_basic", "client_id" : "bd23ca7b376b4bb7a17680a496048473", "introspect_tokens" : true, "client_secret_expires_at" : 0, "scope" : "openid profile email general", "etag" : "ax5TWj+MkZm0Uybao5cBBA==", "client_id_issued_at" : 1558514044, "client_secret" : "*", "resource_ids" : [ ], "functional_user_id" : "jts_user", "client_name" : "/jts", "response_types" : [ "code", "token", "id_token token" ], "preauthorized_scope" : "openid profile email general" } ]
- Change directory to
- While in edit mode, change the Client Secret value and save the file
- Edit the following parameter
"client_secret" : "*"
- TO
"client_secret" : "NewClientSecret"
- Edit the following parameter
- On the JAS server
- Change directory to
[JAS_HOME]\cliand run the following command./ldclient -a https://JazzAuthServerURI/oidc/endpoint/jazzop -u [AdminUser]:[AdminPassword] jts.json
- Change directory to
OR Update Client Secret Using JAS Web UI
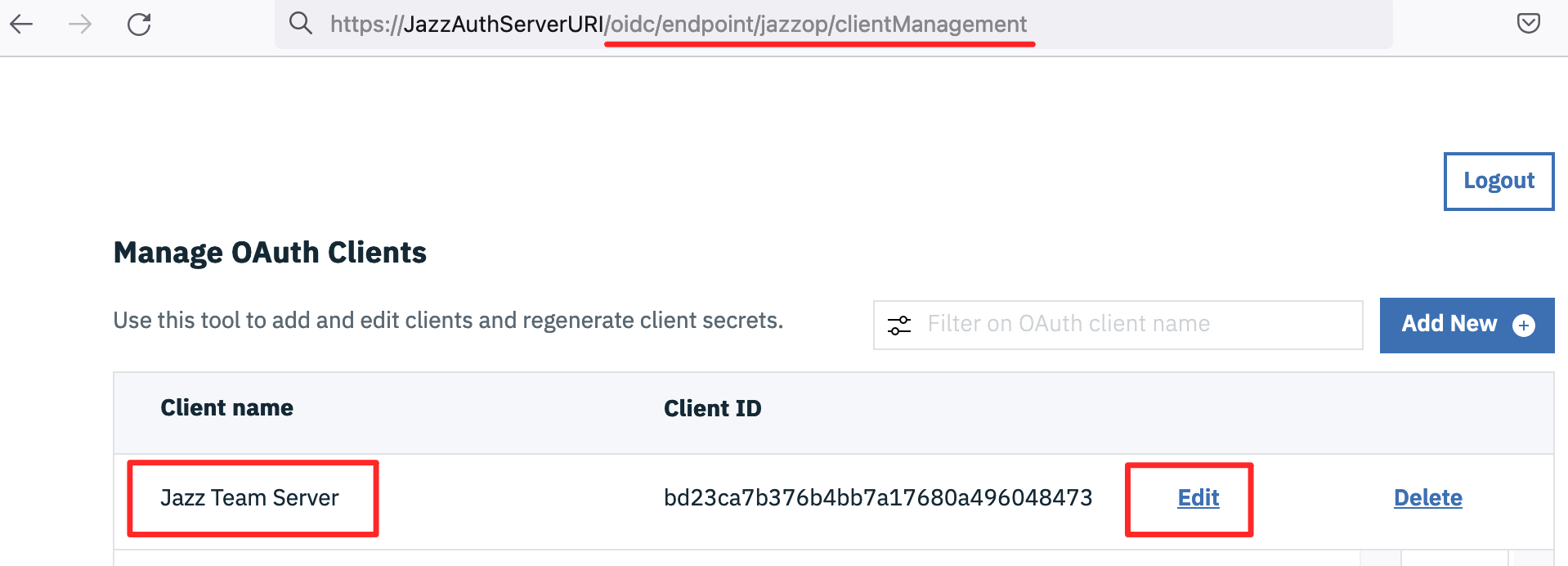
In Jazz Authorization Server version 7.0.2 or higher you could use the Liberty client management UI to update Client registration data. (Not recommended in earlier versions due to a Liberty defect).Following are the instructions to update ClientSecret for JTS application.
- Access JAS URL
https://JazzAuthServerURI/oidc/endpoint/jazzop/clientManagementand login as an Admin User - Click
Editnext to the Client nameJazz Team Server(or the application you intend to change the Client secret)
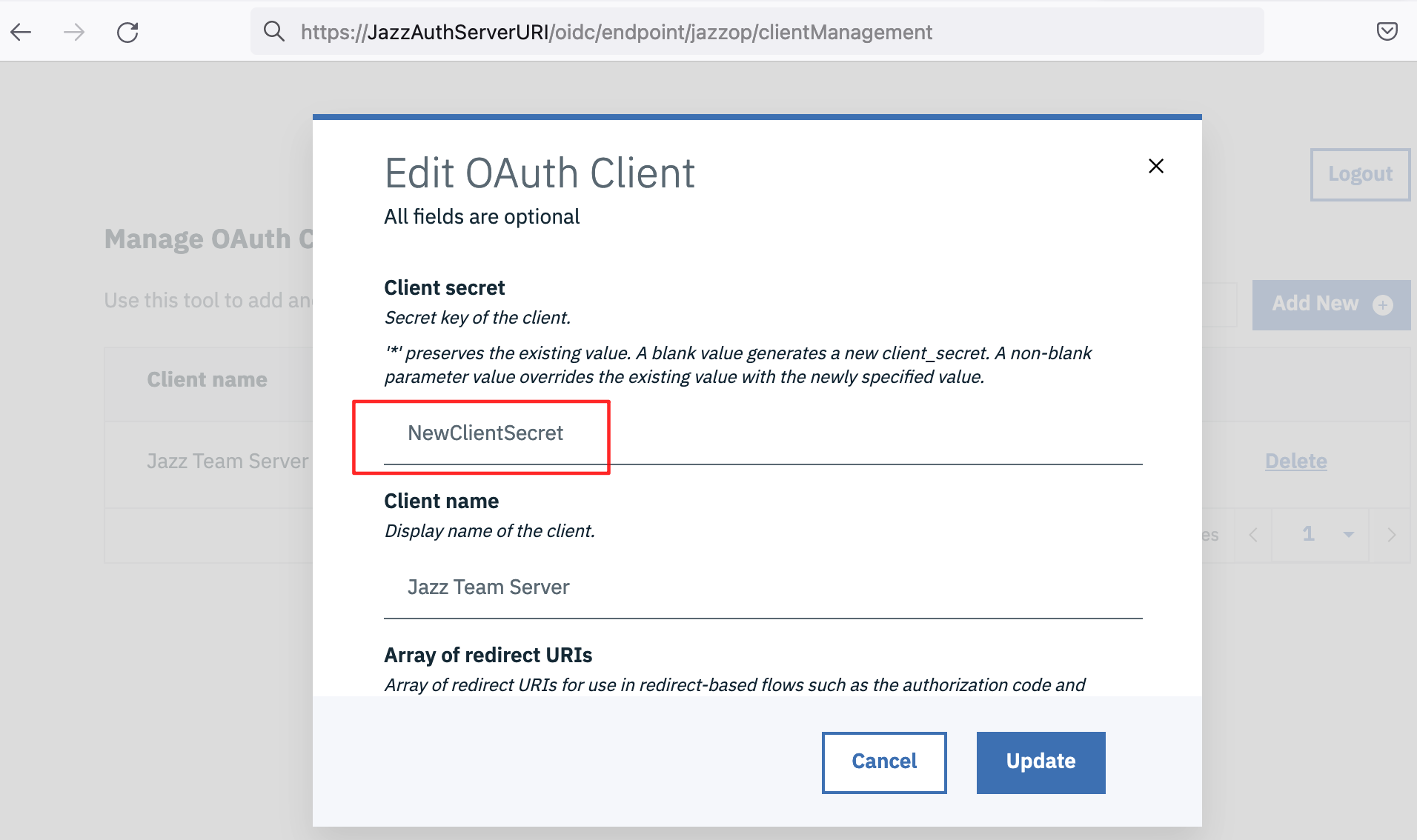
- Modify the value for
Client secretfrom*to secret of your choice and clickUpdate
Update Client Secret in ELM Application
The ClientId and ClientSecret values can be found in each applications properties file. Following are the steps to update the Client Secret for JTS application- Switch to the JTS server and stop the JTS application server
- Edit
[JTS_HOME]\server\conf\jts\teamserver.propertiesfile - Update the following
com.ibm.team.repository.servlet.sso_clientSecret=[Encryptedvalue]TOcom.ibm.team.repository.servlet.sso_clientSecret=NewClientSecret - Start JTS server and test login
Related topics: Jazz Authorization Server, Migrating JAS Servers
Contributions are governed by our Terms of Use. Please read the following disclaimer.
Dashboards and work items are no longer publicly available, so some links may be invalid. We now provide similar information through other means. Learn more here.