Recommended Application Lifecycle Management (ALM) deployment topologies 6.0.0 to 6.0.4
Authors: StevenBeard, DavidChadwick, ThomasPiccoliBuild basis: CLM and SSE 6.0.0 to 6.0.4
Recommended topologies overview
This page describes the Recommended ALM Deployment Topologies for version 6.0.0 to 6.0.4. Refer to Standard deployment topologies overview for high-level description of the standard topologies, how they are categorized and their key characteristics. These recommended deployment topologies for the Rational solution for Application Lifecycle Management (ALM) are a subset of the standard ALM deployment topologies. For the rest of the standard topologies, see Alternative ALM deployment topologies 6.x. Within this wiki, additional guidance and best practices will be developed about how to best instantiate these recommended topologies.Introduction and approach
These recommended topologies were chosen based on the following criteria:- Those that are most commonly and successfully deployed to date by customers and internally within IBM
- Those that are based upon the most commonly available platforms, operating systems and middleware
- Those that are based upon technologies that customers, partners and the IBM Rational Field have the most experience with
- Those that are the focus of testing within IBM Rational.
Recommended topologies
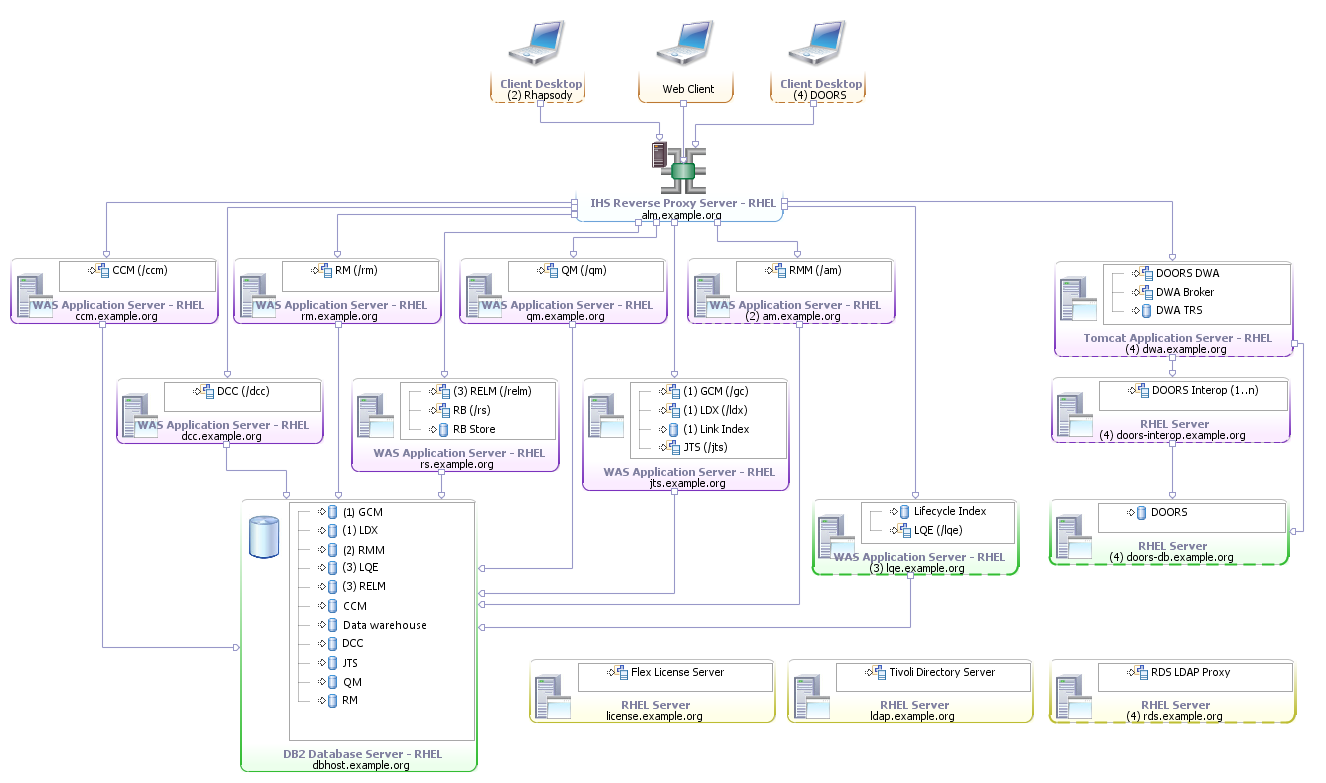
(ALM-E1) Enterprise - Distributed / Linux / DB2
This enterprise topology uses Linux for the server operating systems. It includes both DNG and DOORS/DWA as the RM applications. The applications are distributed across separate servers and WAS instances. A reverse proxy is used to ensure public URI stability. DB2 is used for the databases and is hosted on a separate server. Finally, licenses are served by a floating license server and Tivoli Directory Server provides the LDAP based user management, for all but DOORS/DWA, which uses Windows Active Directory Server. Note that the VVC application is only present in release 6.0 and has been incorporated in other applications in later releases. Additionally, Rhapsody Model Manager, first available in version 6.0.5, is now the recommended architecture management tool. If Rhapsody Design Manager continues to be used, it should be deployed on its own server.| Metadata Variable | Value |
| Operating System | Linux |
| Database Management System | DB2 |
| Application Server | WAS |
| License Management System | Floating |
| User Management System | Tivoli Directory Server |
| Other technologies | Reverse Proxy |
- ALM-E1 Topology Diagram for v6.x:
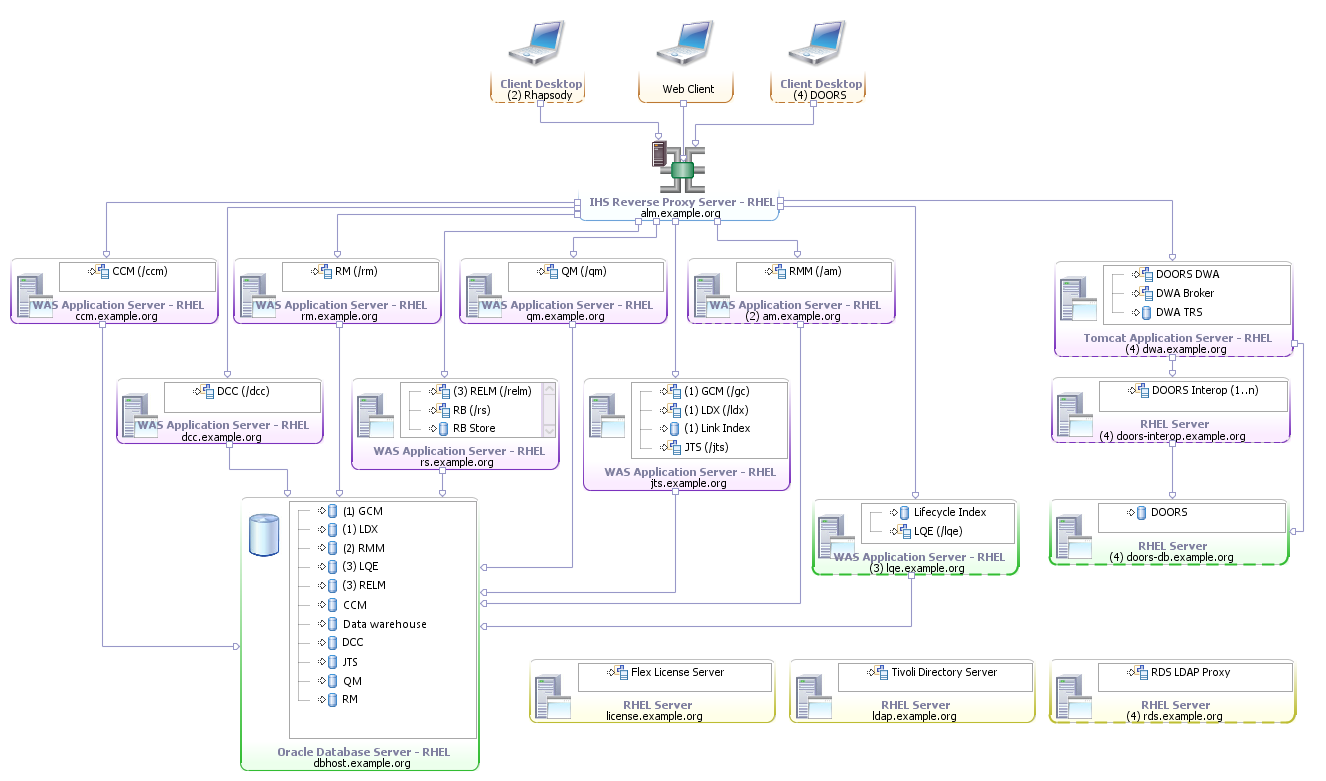
(ALM-E3) Enterprise - Distributed / Linux / Oracle
This enterprise topology uses Linux for the server operating systems. It includes both DNG and DOORS/DWA as the RM applications. The applications are distributed across separate servers and WAS instances. A reverse proxy is used to ensure public URI stability. Oracle is used for the databases and is hosted on a separate server. Finally, licenses are served by a floating license server and Tivoli Directory Server provides the LDAP based user management, for all but DOORS/DWA, which uses Windows Active Directory Server. Note that the VVC application is only present in release 6.0 and has been incorporated in other applications in later releases. Additionally, Rhapsody Model Manager, first available in version 6.0.5, is now the recommended architecture management tool. If Rhapsody Design Manager continues to be used, it should be deployed on its own server.| Metadata Variable | Value |
| Operating System | Linux |
| Database Management System | Oracle |
| Application Server | WAS |
| License Management System | Floating |
| User Management System | Tivoli Directory Server |
| Other technologies | Reverse Proxy |
- ALM-E3 Topology Diagram for v6.x:
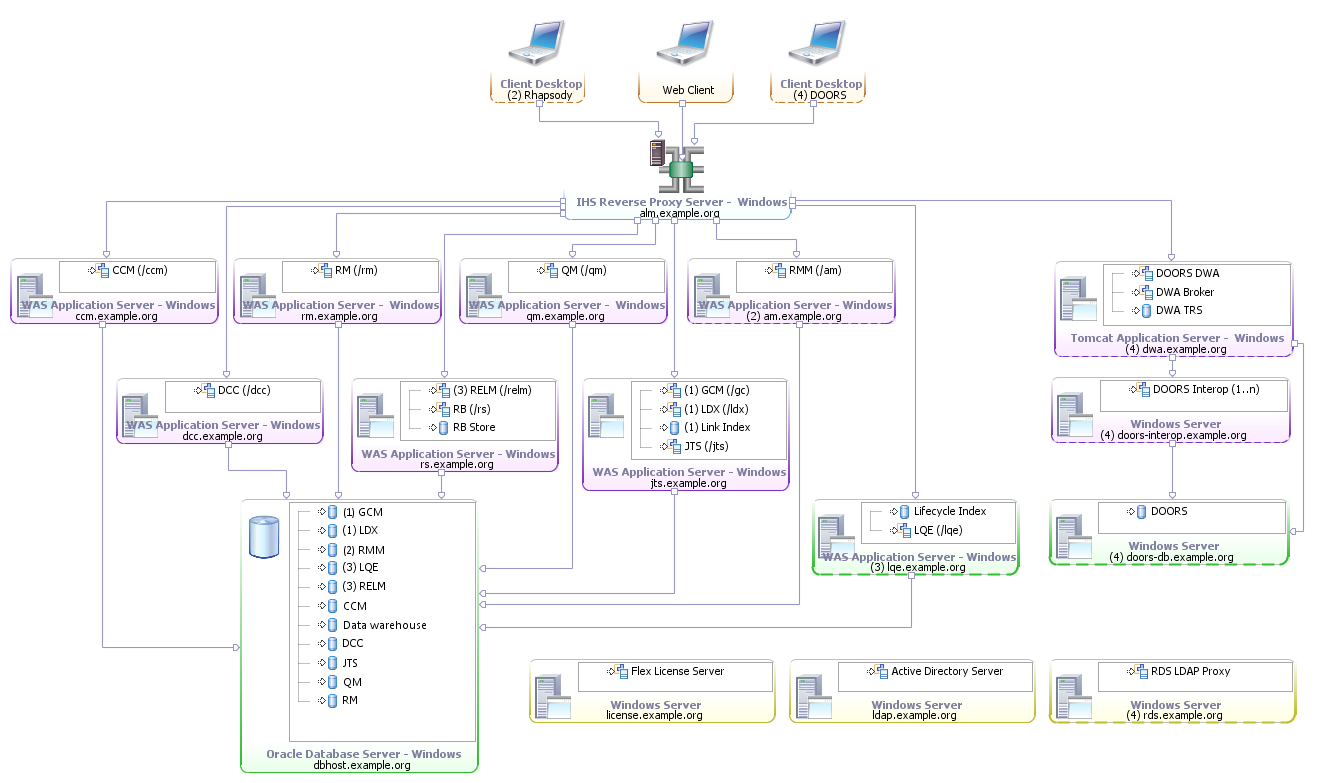
(ALM-E7) Enterprise - Distributed / Windows / Oracle
This enterprise topology uses Windows for the server operating systems. It includes both DNG and DOORS/DWA as RM applications. The applications are distributed across separate servers and WAS instances. A reverse proxy is used to ensure public URI stability. Oracle is used for the databases and is hosted on a separate server. Finally, licenses are served by a floating license server and Windows Active Directory Server provides the LDAP based user management. Note that the VVC application is only present in release 6.0 and has been incorporated in other applications in later releases. Additionally, Rhapsody Model Manager, first available in version 6.0.5, is now the recommended architecture management tool. If Rhapsody Design Manager continues to be used, it should be deployed on its own server.| Metadata Variable | Value |
| Operating System | Microsoft Windows |
| Database Management System | Oracle |
| Application Server | WAS |
| License Management System | Floating |
| User Management System | Microsoft Active Directory Server |
| Other technologies | Reverse Proxy |
- ALM-E7 Topology Diagram for v6.x:
Applying the topologies
Every customer's environment is different with unique, necessary and often immutable requirements and constraints. We recognize that these standard topologies may not provide enough detail to make them immediately implementable in some customer environments, but we wanted to describe several topologies with enough variability to give an indication of what is possible and where our recommendations start. While we recommend customers start with a standard topology that is most applicable to them, we recognize they will need to make changes and customizations to support their own unique requirements and constraints. IBM will support your own implementations, but may ask you to describe which topology is most applicable to your deployment and ask you to document what is unique in your environment to expedite any potential support situation. To aid you in documenting your chosen deployment topology, we have made the following Rational Software Architect (RSA) model files available: These may be imported into RSA then further modified or expanded to represent your environment. Look at the Installation_Instructions.txt file for information on how to import the models into RSA.Datasheets and sizing guidelines
Find ALM-specific performance datasheets, sizing guidelines and performance-related case studies on the Performance datasheets and sizing guidelines page.Next steps
This topic is meant to briefly introduce these standard topologies and describe how they might be applied. Work is already underway to build upon and apply them. Subsequent updates to this topic and supporting topics will provide additional insight into their usage. Future updates to this topic or supporting topics may cover:- Deeper look at select topologies
- Provide suggested tuning parameters
- Consider high availability database topologies
- Begin to expand this topology model into other domains
- Discussion of strategic integrations with other IBM and non-IBM products.
Related topics: Alternative ALM deployment topologies 6.x, Standard deployment topologies overview
Additional contributors: IanCompton
Contributions are governed by our Terms of Use. Please read the following disclaimer.
Dashboards and work items are no longer publicly available, so some links may be invalid. We now provide similar information through other means. Learn more here.