r8 - 2021-08-13 - 08:38:32 - ShubjitNaikYou are here: TWiki >  Deployment Web > DeploymentInstallingUpgradingAndMigrating > JazzAuthorizationServer > LogoutJASSAMLOIDC
Deployment Web > DeploymentInstallingUpgradingAndMigrating > JazzAuthorizationServer > LogoutJASSAMLOIDC
uc Authors: ShubjitNaik
Build basis: Engineering Lifecycle Management and Jazz Authorization Server 7.0.2 and Higher
Build basis: Engineering Lifecycle Management and Jazz Authorization Server 7.0.2 and Higher
Jazz Authorization Server (JAS) is a Liberty OpenID Connect Provider and it can be configured to further delegate authentication to a SAML Identity Provider or a Third Party OIDC Provider. The expectation is for Single Sign-On and Sign-Out to work between ELM and non-ELM applications that are both configured to use the same Provider.
The focus on this Article is on Single Sign-On and Logout. It is assumed that you have configured JAS with either a SAML IdP or a Third Party OIDC Provider.
Increasing the Request Field Size on IBM HTTP Server
This workaround would work if you can directly access the SAML or OIDC Logout URL
Note: The following is found to work with ELM and JAS 7.0.2. This is not an officially tested and supported method.
Configuring Single Sign-On
When configured with a Third Party OIDC Provider, no changes are needed. The default configuration of Jazz Authorization Server configured with SAML IdP indicates the IdP to force the user to re-authenticate. We would need to change this configuration for SSO to work between ELM and Non-ELM applications. Steps to update the configuration:- Edit
appConfig.xmlfile located at[JAS_HOME]\wlp\usr\server\jazzop\appConfig.xml - Search for
samlWebSso20section and update the parameter forceAuthn to forceAuthn="false" and add parameter spLogout="true"<samlWebSso20 id="defaultSP" spCookieName="jazzop_sso_cookie_idp" forceAuthn="false" authFilterRef="samlAuthFilter" spLogout="true" > </samlWebSso20> - Test Single Sign-On between ELM and Non-ELM applications
Configuring Single Sign-Out
With the default configurations the Logout operations from ELM does not complete. You would need to perform the following additional configuration in ELM.- Request your Administrator to share the SAML or OIDC Logout URL
- Example Microsoft ADFS federation logout URL
https://[AFDF_Server]/adfs/ls/?wa=wsignout1.0
- Example Microsoft ADFS federation logout URL
- In each ELM application
jts, ccm, qm, rm, gc and dccperform the following:- Access Advanced Properties
https://[ELM_URL]/[app]/admin#action=com.ibm.team.repository.admin.configureAdvanced - Search for the property
Web Logout URIand update the value to the Logout URL received - Search for the property
Trusted URIs for client authorization and redirectionand update the value with the Logout URL received
- Access Advanced Properties
- Test Logout from ELM Applications
Testing
After applying the Single Sign-On and Sign Out configurations mentioned in the previous steps, following are the results- Single Sign-On is achieved between ELM and Non-ELM applications
- Logout from an ELM Application will logout via the IdP logout URL and all other ELM Applications are logged out
- Logout from a Non-ELM application - ELM applications are NOT logged out immediately
- Post the SSO timeout which is set to 2 hours by default (can be changed), the applications are redirected to the IdP and existing sessions are logged out
Troubleshooting
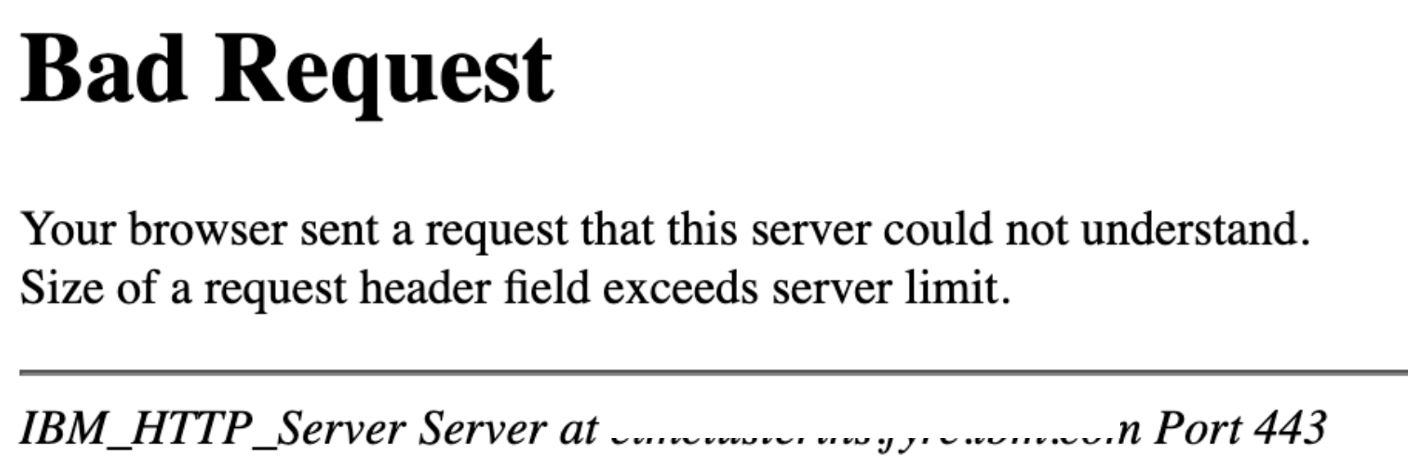
Error: Bad Request
If you encounter the following error, you would need to increase the Request Field size limit on the Reverse Proxy server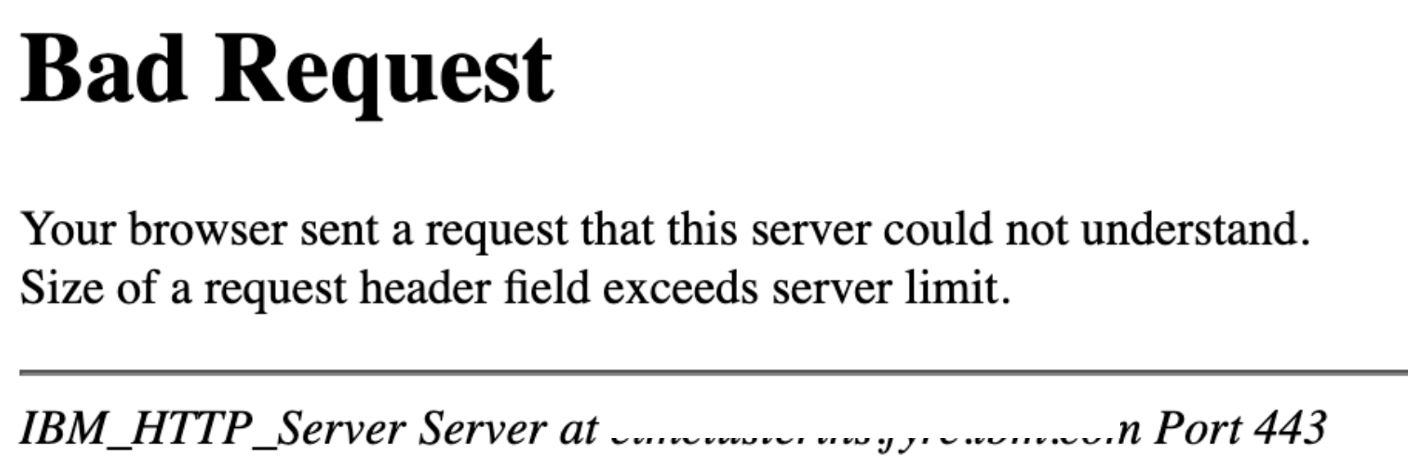
Increasing the Request Field Size on IBM HTTP Server
- Edit the file
[IHS_HOME]\conf\httpd.conf - Add the parameter
LimitRequestFieldSize 16380along with section that define ThreadLimit
Related topics: Jazz Authorization Server Landing Page, Configure ELM with a Third Party OIDC provider
External links:
-
 Deployment web
Deployment web
-
 Planning and design
Planning and design
-
 Installing and upgrading
Installing and upgrading
-
 Migrating and evolving
Migrating and evolving
-
 Integrating
Integrating
-
 Administering
Administering
-
 Monitoring
Monitoring
-
 Troubleshooting
Troubleshooting
-
 To do
To do
-
 Under construction
Under construction
-
 New
New
-
 Updated
Updated
-
 Constant change
Constant change
- None - stable page
- Smaller versions of status icons for inline text:
-





Contributions are governed by our Terms of Use. Please read the following disclaimer.
Dashboards and work items are no longer publicly available, so some links may be invalid. We now provide similar information through other means. Learn more here.